
Conversational Linux management is emerging as a powerful way for administrators to interact with systems using natural language instead of complex command syntax.
By combining AI with traditional Linux tooling, organizations can improve operational efficiency while maintaining strict controls such as logging, approvals, and least privilege access.
A senior administrator can diagnose a Linux issue in seconds.
A new team member may spend hours trying to remember the exact command sequence.
The difference isn’t intelligence.
It’s documentation — or more precisely, the lack of it.
Across many organizations, Linux expertise lives in scattered runbooks, internal notes, and the memory of a few experienced operators. When those individuals are unavailable, routine tasks slow down dramatically.
That operational friction has fueled growing interest in conversational Linux management — systems that allow administrators to interact with infrastructure through natural language instead of memorized command syntax.
The idea sounds deceptively simple:
“Show me servers with disk usage above 90%.”
“Restart the web service on node three.”
“Generate a report of failed login attempts.”
Under the hood, those requests translate into controlled system operations.
But the promise of conversational administration comes with an important caveat.
Automation must never bypass operational safeguards.
When implemented correctly, conversational systems sit on top of the same guardrails that already protect Linux infrastructure: change control, audit logging, approvals, and least privilege access.
The result isn’t replacing administrators.
It’s reducing friction between operators and systems like Linux, allowing teams to execute routine operations faster while maintaining the controls enterprise environments require.
Understanding how to design that balance is the key to making conversational infrastructure practical.
Why Conversational Linux Management Is Emerging
Many organizations underestimate how manageable Linux environments become once standardized tooling and automation frameworks are in place.
Linux was designed around scriptability and composability.
Those characteristics make large-scale administration more predictable than many teams expect.
Standardized Toolchains
Linux environments typically rely on well-established operational tools such as:
- Bash for scripting
- SSH for secure remote access
- Cron for scheduled tasks
These components create a consistent operational foundation.
A script written for one system can often run across thousands of servers with minimal modification.
Infrastructure as Code
Modern DevOps practices extend this philosophy further.
Infrastructure configuration is often managed through automation platforms such as:
- Ansible
- Terraform
These tools convert infrastructure management into version-controlled code.
Instead of manually configuring systems, administrators define desired system states.
Predictable System Behavior
Because Linux systems rely heavily on configuration files and documented processes, changes can be tracked precisely.
Logs, version control, and configuration management provide a transparent operational history.
Operational takeaway:
Linux environments become easier to manage at scale once operational practices shift from manual commands to automated workflows.
Conversational Interfaces: A New Layer for Infrastructure Operations
Conversational interfaces build on top of existing automation.
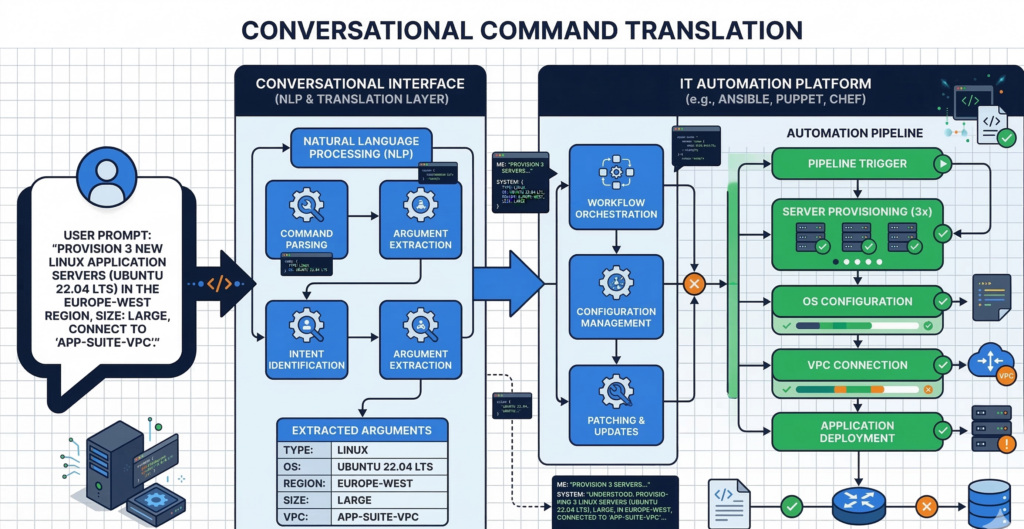
Instead of running scripts manually, administrators interact with infrastructure through natural language commands.
The system then translates those instructions into structured operations.
Translating Language Into Actions
For example:
“List servers with CPU usage above 80%.”
A conversational management system might translate that request into:
- a monitoring query
- a system report
- or an alert investigation workflow
Underneath the interface, the same infrastructure tools still perform the work.
Accelerating Routine Operations
Many administrative tasks are repetitive:
- checking service status
- gathering logs
- restarting applications
- querying system metrics
Conversational systems dramatically reduce the friction involved in executing these tasks.
Instead of recalling command syntax, administrators describe the outcome they want.
Documentation Becomes Executable
One powerful side effect of conversational management is that documentation can become operational logic.
Runbooks describing common procedures can be embedded directly into conversational workflows.
For example:
“Investigate high memory usage on server 12.”
The system may follow a predefined troubleshooting workflow automatically.
Organizations experimenting with conversational infrastructure often integrate internal documentation, operational procedures, and automation scripts into secure AI systems. Platforms like Aivorys (https://aivorys.com) enable organizations to deploy private AI assistants connected to internal knowledge bases and operational tools, allowing teams to execute workflows conversationally without exposing sensitive operational data externally.
Operational takeaway:
Conversational interfaces reduce cognitive load by turning documentation and automation scripts into accessible workflows.
Guardrails: Why Conversational Management Requires Strong Controls
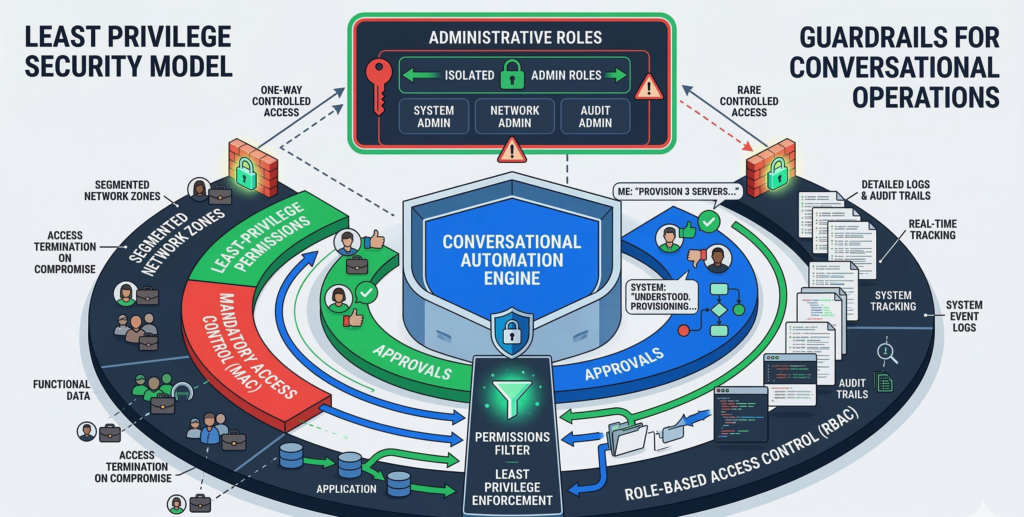
Natural language interfaces create a new risk.
Commands may be easier to execute — but that convenience must not weaken operational safeguards.
Three guardrails are essential.
Approval Workflows
Certain infrastructure actions should always require approval.
Examples include:
- deploying configuration changes
- restarting production services
- modifying access permissions
Conversational systems should trigger approval requests rather than executing these actions automatically.
Audit Logging
Every conversational command should generate structured logs.
Logs must capture:
- the user issuing the request
- the interpreted command
- the resulting system actions
This transparency ensures organizations maintain compliance and traceability.
Role-Based Access Control
Not every administrator should have the same capabilities.
A conversational interface must respect existing role-based access policies.
For example:
- junior administrators may retrieve logs
- senior engineers may restart services
- infrastructure architects may modify system configurations
Operational takeaway:
Conversational management must inherit existing security policies rather than bypass them.
The Principle of Least Privilege in AI-Assisted Operations

Least privilege becomes even more important when automation is involved.
A conversational system executing commands on behalf of administrators must operate within tightly defined permissions.
Scoped Automation
Automation tools should execute tasks using restricted service accounts.
Each automation capability should have a clearly defined scope.
Examples include:
- log retrieval
- monitoring queries
- limited service restarts
This ensures compromised automation systems cannot control entire environments.
Command Whitelisting
Organizations can further reduce risk by defining allowed command sets.
Conversational systems may translate user intent into commands — but only commands on approved lists should execute.
Environment Segmentation
Conversational tooling should distinguish between environments such as:
- development
- staging
- production
Production systems may require additional safeguards.
Operational takeaway:
Conversational infrastructure must operate under the same least privilege principles that protect traditional system administration.
Logging, Change Tracking, and Rollback in Conversational Operations
Modern infrastructure management relies on observability and traceability.
Conversational interfaces should strengthen these capabilities rather than obscure them.
Structured Change Tracking
Every conversational action should generate structured events.
These events may include:
- command interpretation logs
- infrastructure changes
- configuration modifications
Centralized logging platforms such as Elastic Stack or Grafana often aggregate these logs for analysis.
Rollback and Safety Nets
Automation systems should support rapid rollback of unintended changes.
Rollback strategies may include:
- version-controlled configuration files
- infrastructure snapshots
- automated recovery scripts
This ensures conversational automation does not introduce irreversible changes.
Observability Across the Stack
Monitoring platforms allow teams to verify that conversational actions produce the intended results.
Metrics, alerts, and logs help validate system behavior after automated changes.
Operational takeaway:
Conversational operations must improve visibility rather than obscure system activity.
Safe Operating Model for Conversational Linux Management
Organizations exploring conversational administration should adopt a structured operating model.
The following framework provides a practical baseline.
Conversational Infrastructure Readiness Checklist
Operational Foundation
- configuration management tools manage infrastructure state
- infrastructure changes are version controlled
- system monitoring provides visibility into performance
Conversational Interface Controls
- commands translate to predefined automation workflows
- sensitive operations require approval workflows
- user permissions restrict available actions
Security Controls
- automation uses least privilege service accounts
- command execution is logged and auditable
- infrastructure environments remain segmented
Safety and Recovery
- rollback mechanisms exist for automated changes
- system snapshots or backups are maintained
- operational runbooks define incident response steps
Organizations deploying managed infrastructure environments sometimes focus on making complex systems easier for operators to manage without weakening security practices. Providers such as Carefree Computing often emphasize usability improvements alongside structured operational controls so administrative efficiency increases without expanding risk.
Practical takeaway:
Conversational infrastructure works best when it accelerates existing operational workflows rather than replacing them.
Frequently Asked Questions
What is conversational Linux management?
Conversational Linux management refers to infrastructure tools that allow administrators to interact with servers using natural language commands. Instead of manually executing complex command sequences, administrators describe the desired outcome and the system translates that request into structured automation workflows.
Can conversational interfaces safely manage production infrastructure?
Yes, but only when combined with strong operational controls. Safe implementations include role-based access control, approval workflows for sensitive actions, detailed audit logs, and rollback mechanisms. These safeguards ensure that natural language commands cannot bypass established change management policies.
How does conversational infrastructure improve productivity?
Conversational systems reduce the cognitive overhead involved in remembering command syntax or searching documentation. Administrators can request system information, execute troubleshooting workflows, or retrieve logs using natural language, which accelerates routine operational tasks.
Do conversational systems replace Linux administrators?
No. These systems act as operational interfaces rather than decision-makers. Experienced administrators still design infrastructure, define automation workflows, and approve sensitive changes. Conversational tooling simply provides a faster way to interact with those systems.
What risks do conversational infrastructure tools introduce?
The primary risks involve unauthorized commands, automation misuse, and insufficient auditing. Organizations mitigate these risks through least privilege policies, command whitelisting, approval workflows, and comprehensive logging systems that record all actions performed through conversational interfaces.
Conclusion
Linux administration has always rewarded precision.
Commands must be correct. Configurations must be documented. Changes must be traceable.
Conversational infrastructure doesn’t eliminate those requirements.
Instead, it moves complexity beneath the surface, allowing administrators to interact with systems in a more intuitive way while automation handles the mechanics.
The organizations that benefit most from this shift are not those chasing convenience.
They are the ones that pair conversational interfaces with strong operational discipline — structured automation, strict access control, comprehensive logging, and reliable rollback strategies.
When those foundations exist, conversational Linux management becomes something powerful.
Not a shortcut.
But a more efficient way to operate infrastructure responsibly.
