Conversational Linux Management: How AI Is Changing Linux Administration

Conversational Linux management is emerging as a powerful way for administrators to interact with systems using natural language instead of complex command syntax. By combining AI with traditional Linux tooling, organizations can improve operational efficiency while maintaining strict controls such as logging, approvals, and least privilege access. A senior administrator can diagnose a Linux issue […]
Windows Software Supply Chain Problem: Signed ≠ Safe

Windows software supply chain security has become a major concern for enterprises as attackers increasingly exploit trusted software, signed drivers, and update mechanisms. When malicious code enters the ecosystem through legitimate channels, traditional security tools struggle to detect it. Understanding how supply chain weaknesses impact Windows endpoints is now critical for modern security architecture. Attackers […]
Endpoint Security Strategy: Why Antivirus Is No Longer Enough

A modern endpoint security strategy must address threats that traditional antivirus can no longer stop. Today’s attackers use fileless malware, privilege escalation, and sophisticated bypass techniques that easily evade signature-based detection. Organizations that rely only on antivirus are operating with an outdated security model. A helpdesk ticket arrives: an employee can’t install a required application. […]
Secure Browsing on Linux: How to Reduce Phishing and Drive-By Risk Without “Security Theater”
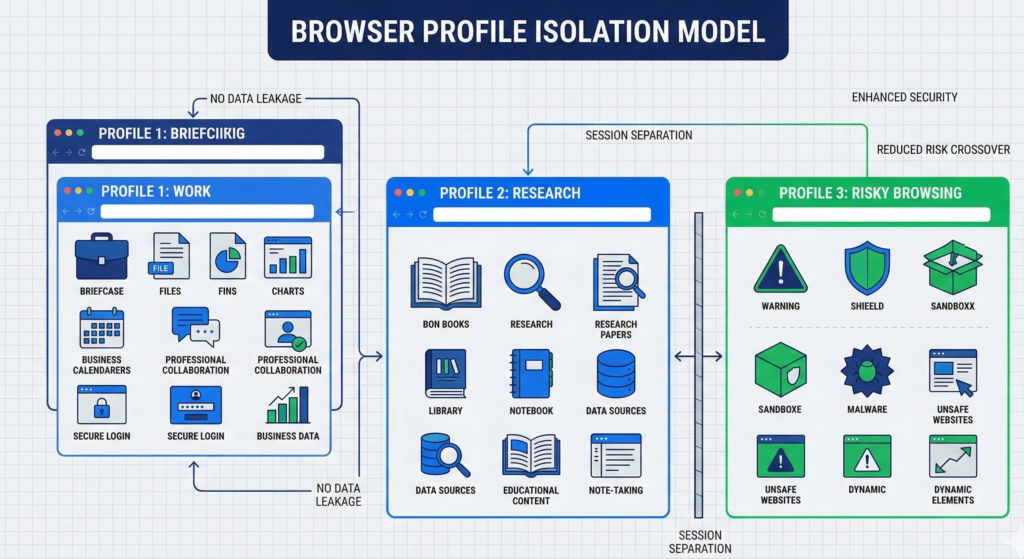
Most organizations still treat the operating system as the center of security. That assumption is outdated. The browser has quietly become the real operating system for modern work. Email runs in the browser.CRM platforms run in the browser.Internal dashboards, file storage, support tools, and analytics all live in browser tabs. Which means most compromises now […]
Backup Strategy for Migrations: Prevent Data Loss & Ransomware

Most people discover they don’t have real backups after they need them. A migration fails. A laptop dies mid-upgrade. A ransomware attack encrypts a server. Someone says, “Don’t worry — everything is backed up.” Then the uncomfortable discovery happens. The backup hasn’t run in months.The restore process fails.Critical data was never included. Or worse — […]
The Windows 10 End-of-Support Reality: A Security Decision, Not a UI Preference

Unsupported operating systems are the infrastructure equivalent of unlocked doors. They still function. Employees still log in. Applications still open. But the moment security updates stop, the system quietly becomes one of the most attractive entry points in your entire environment. That’s exactly the situation approaching with Microsoft Windows 10, whose official support from Microsoft […]
