Security headlines often celebrate progress. New isolation layers. Stronger signing requirements. Expanded endpoint telemetry.
Yet Windows security bypasses continue to surface—particularly at the kernel boundary. Attackers repeatedly exploit driver vulnerabilities, legacy compatibility mechanisms, or privileged execution paths to neutralize defenses from underneath.
Improvement is not the same as closure. A system can become more secure overall while preserving a handful of structural seams that remain highly valuable to adversaries.
For IT leaders, this creates confusion. If Windows security keeps adding controls, why do kernel-adjacent bypass classes keep working? The answer lies in backward compatibility, trust boundaries, and the limits of detection-only strategy.
This article breaks down the structural dynamics behind recurring bypass patterns and provides a practical control map: prevent → contain → detect.
Backward Compatibility and Trust Boundaries
Windows carries decades of ecosystem history. Enterprises depend on legacy drivers, specialized hardware integrations, vertical-market software, and deeply embedded workflows.
That backward compatibility is a feature. It is also a constraint.
Compatibility Preserves Attack Surface
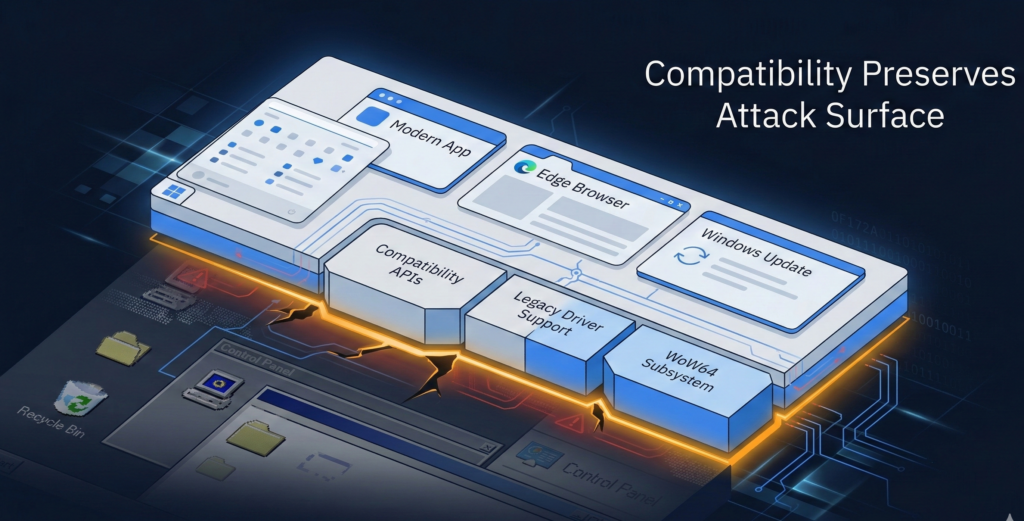
Many kernel-adjacent bypasses exploit:
- Older driver interfaces still supported for enterprise stability
- Legacy IOCTL handling in signed drivers
- Backward-compatible service permissions
- Trusted but outdated components
Micro-insight: Every compatibility guarantee extends the lifespan of potential trust boundary weaknesses.**
Removing these seams outright would break business operations. So they remain—carefully managed, but not eliminated.
Trust Is Evaluated at Load Time, Not Intent
Driver signing ensures code origin, not runtime safety. Once a signed driver loads, the kernel assumes cooperative behavior unless restricted by additional policies.
Security research and incident response reports consistently show attackers exploiting signed but vulnerable components. The operating system verifies authenticity, not exploitability.
Actionable Takeaway
Inventory legacy dependencies. Identify which kernel-mode components are business-critical versus historically inherited. Compatibility should be intentional, not accidental.
[INTERNAL LINK: Windows driver risk management framework]
Kernel Access as the Attacker’s True Objective
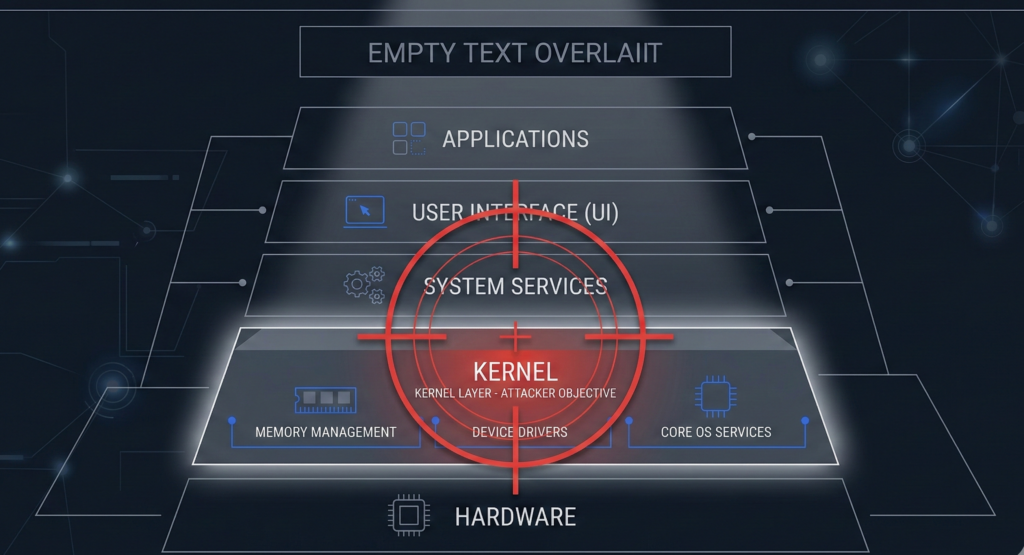
Attackers do not chase novelty. They chase leverage.
Why the Kernel Matters
Kernel access allows:
- Disabling EDR callbacks
- Manipulating memory directly
- Removing process protections
- Elevating privileges to SYSTEM
- Hiding malicious artifacts from user-mode tools
Once the kernel boundary collapses, detection tools lose structural authority.
Micro-insight: Kernel compromise shifts defenders from prevention to damage control.**
This is why techniques like BYOVD persist. Even as controls improve, the payoff for kernel access remains enormous.
Recurring Abuse Patterns
Trendlines in security reporting show a pattern:
- Initial foothold via phishing or exposed service
- Local privilege escalation
- Driver-based or kernel-adjacent bypass
- Security tool impairment
- Lateral movement and domain encryption
The tactic evolves. The goal does not.
Actionable Takeaway
Treat kernel access as a defined adversary objective in your threat model. If your security roadmap does not explicitly address it, it remains an unmodeled risk.
Why Detection-Only Strategies Fail Under Bypass Pressure
Many organizations invest heavily in telemetry. Logs, alerts, machine learning classifiers. Detection improves yearly.
But detection depends on visibility.
The Fragility of Visibility
If kernel-level manipulation can:
- Blind telemetry
- Disable agents
- Modify logs before transmission
Then detection becomes probabilistic rather than deterministic.
Micro-insight: You cannot detect what your monitoring layer cannot see.**
The Illusion of Tool Stacking
Adding more EDR agents does not solve a compromised trust boundary. If the kernel layer is subverted, stacked tools may share the same blind spot.
Research consistently shows that layered defense works only when layers are architecturally independent—not co-dependent within the same privilege domain.
Governance and Control in Sensitive Environments
Organizations deploying internal AI systems, automation workflows, or voice-driven intake platforms should be particularly cautious. Platforms like Aivorys (https://aivorys.com) are often deployed in environments where proprietary knowledge bases, CRM integrations, and workflow automation are central to operations. A kernel-level bypass on endpoints interacting with such systems must be assumed possible and contained by design.
Actionable Takeaway
Prioritize preventive and containment controls alongside detection. Detection should confirm resilience, not compensate for structural exposure.
[INTERNAL LINK: Designing layered endpoint security architecture]
The Control Map: Prevent → Contain → Detect
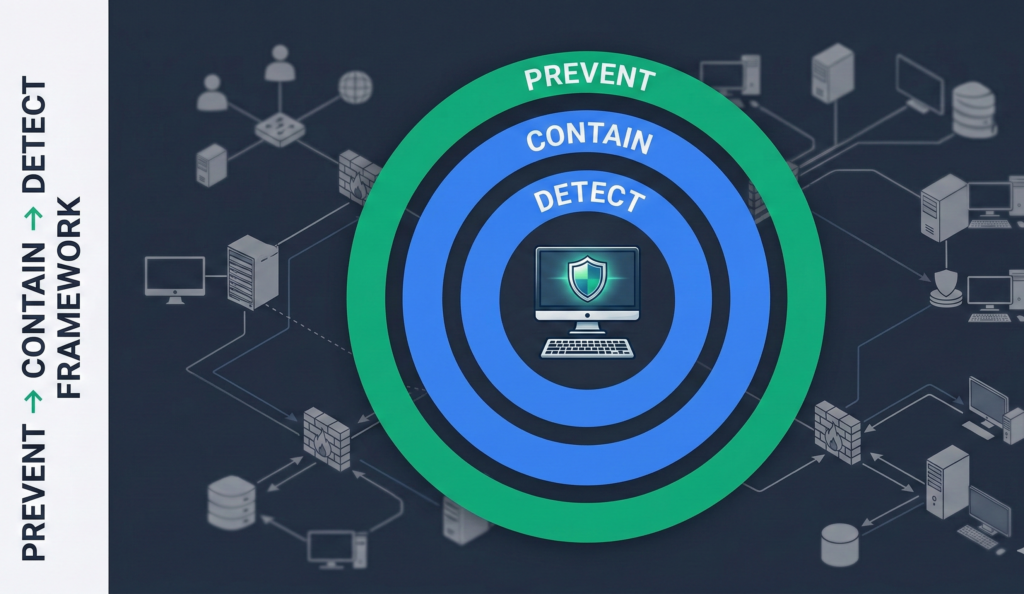
This framework provides structural clarity.
1. Prevent: Reduce Probability of Kernel Compromise
Focus on reducing the likelihood of successful bypass.
- Enforce least privilege; eliminate persistent local admin
- Restrict driver installation via application control policies
- Enable and verify vulnerable driver blocklists
- Remove unnecessary kernel drivers
Prevention is imperfect—but it meaningfully raises attacker cost.
2. Contain: Limit Blast Radius If Compromise Occurs
Assume eventual breach at the endpoint layer.
- Segment workstations from servers
- Restrict east-west traffic
- Enforce credential guard and SMB signing
- Separate administrative tiers
Containment ensures a kernel-level bypass does not become domain-wide catastrophe.
3. Detect: Validate and Respond Rapidly
Detection remains critical, but scoped appropriately.
- Monitor driver load events
- Alert on privilege escalation anomalies
- Correlate endpoint logs with network telemetry
- Conduct periodic compromise simulations
Micro-insight: Mature security strategy is not linear. It is layered and adversary-aware.**
Actionable Takeaway
Score your environment across prevent, contain, and detect. Gaps often cluster around containment, not detection.
[INTERNAL LINK: Privilege reduction roadmap for Windows networks]
Where Windows Security Is Genuinely Improving

Balance is important.
Windows has strengthened:
- Virtualization-based security
- Memory integrity enforcement
- Secure Boot integration
- Hardware-backed credential protection
These controls meaningfully reduce many classes of attack.
However, improvements coexist with compatibility layers. That coexistence preserves certain high-impact bypass classes.
Micro-insight: Progress reduces surface area, but rarely eliminates structural seams entirely.**
Actionable Takeaway
Adopt new protections deliberately—but evaluate them in the context of your compatibility constraints and legacy drivers. Enablement without enforcement validation creates false confidence.
Common Misconceptions About Windows Security Bypasses
“If Microsoft patches it, the risk disappears.”
Patches reduce known vulnerabilities. Attackers pivot to newly discovered or legacy weaknesses that remain supported.
“Only advanced nation-state actors exploit kernel bypasses.”
Ransomware operators increasingly adopt publicly documented techniques once they become reliable and repeatable.
“Detection tools will alert us in time.”
If detection relies on components operating in compromised privilege layers, alerting may be delayed or suppressed.
Correcting these assumptions prevents complacency.
Actionable Takeaway
Treat bypass classes as recurring design challenges, not one-time anomalies.
FAQ Section
Why do Windows security bypasses keep happening?
Windows must preserve backward compatibility for enterprise software and hardware ecosystems. That compatibility maintains legacy interfaces and drivers, some of which can be abused. Improvements reduce risk but rarely eliminate all structural seams attackers target.
What is a kernel-level attack in Windows?
A kernel-level attack gains execution within the Windows kernel, allowing direct interaction with core system components. This can enable disabling security tools, escalating privileges, or hiding malicious activity from user-mode monitoring software.
Does better EDR stop kernel bypass techniques?
EDR improves detection and response, but kernel-level exploitation may disable or blind user-mode agents. Effective defense requires preventive controls, segmentation, and monitoring that does not rely solely on a single privilege domain.
Are legacy drivers a serious security risk?
They can be. Older drivers may contain vulnerabilities that remain exploitable even if properly signed. Organizations should inventory and review kernel drivers regularly to reduce inherited risk.
What is the most effective way to reduce kernel attack impact?
Combine least privilege enforcement, application control for drivers, network segmentation, and active monitoring. No single control is sufficient. The strategy must address prevention, containment, and detection together.
Conclusion
Windows security is not stagnant. It is steadily evolving. Yet kernel-adjacent bypasses persist because compatibility guarantees and trust boundary design preserve narrow but valuable seams.
The strategic mistake is assuming improvement equals immunity.
Security maturity means modeling adversary goals clearly, reducing the probability of kernel compromise, containing impact when prevention fails, and detecting anomalies without over-relying on a single layer.
Modernization is not about stacking more tools. It is about redesigning boundaries so that when one layer bends, the rest of the architecture holds.
The question is not whether Windows is improving. It is whether your defensive model evolves with equal discipline.
