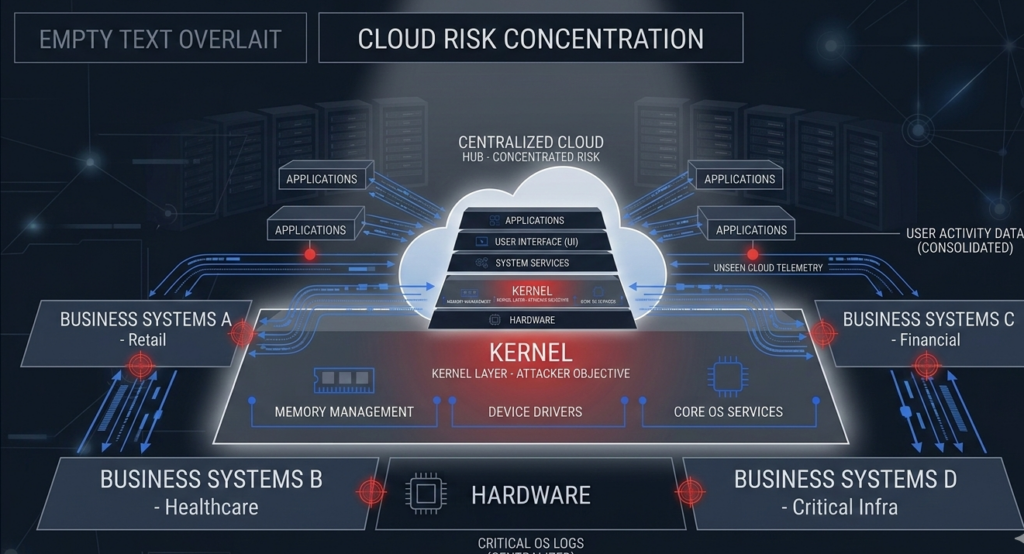
A cloud outage rarely begins in the cloud. It starts in a configuration drift, an unpatched node, a misaligned access policy.
Cloud is not “someone else’s computer.” It is your risk model, running in someone else’s data center. And Linux cloud infrastructure has become the dominant foundation not because of ideology, but because it tolerates pressure without losing control.
When systems scale from ten instances to ten thousand, predictability beats preference. Automation beats manual oversight. Verifiability beats assumption.
Linux won cloud infrastructure because it is controllable, automatable, and stable under stress. This article breaks down the operational mechanics behind that dominance: immutable builds, Infrastructure as Code, fleet patch discipline, kernel security primitives, and the container reality that makes Linux the default substrate of modern platforms.
If you operate production workloads, this is not academic. It is architectural gravity.
Immutable Builds and Infrastructure as Code: Control at Scale
Cloud-native operations depend on repeatability. Linux supports this at the kernel and userland level with minimal hidden state.
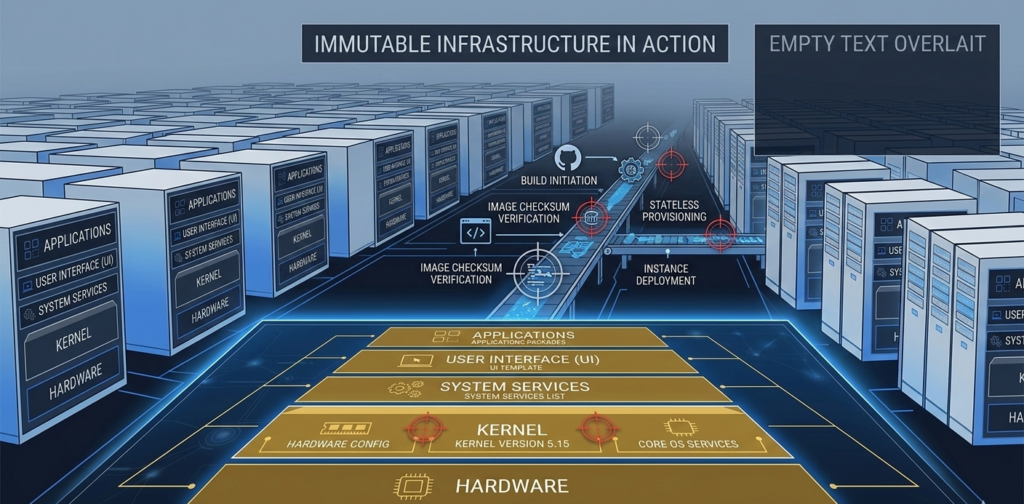
Immutable Infrastructure
Immutable builds treat servers as disposable. You do not patch them in place. You rebuild from a version-controlled image and redeploy.
Linux distributions are structured for this model:
- Minimal base images
- Deterministic package management
- Scriptable configuration
- Transparent service management
Predictability reduces blast radius.
Instead of troubleshooting snowflake servers, teams redeploy known-good images. Drift disappears because drift never accumulates.
Infrastructure as Code (IaC)
Linux integrates cleanly with Terraform, Ansible, and cloud-native provisioning frameworks. Configuration files define:
- Network rules
- OS packages
- Access controls
- Logging endpoints
- Monitoring agents
Everything becomes versioned.
When you combine Linux cloud infrastructure with IaC discipline, audits become diff reviews instead of forensic archaeology.
Competitors often discuss “cloud flexibility” abstractly. What they miss is the operational leverage of deterministic builds.
Actionable takeaway:
Standardize on a minimal Linux base image and enforce image rebuilds rather than in-place patching. Version-control every configuration artifact.
Patch Workflows and Fleet Consistency in Linux Cloud Infrastructure
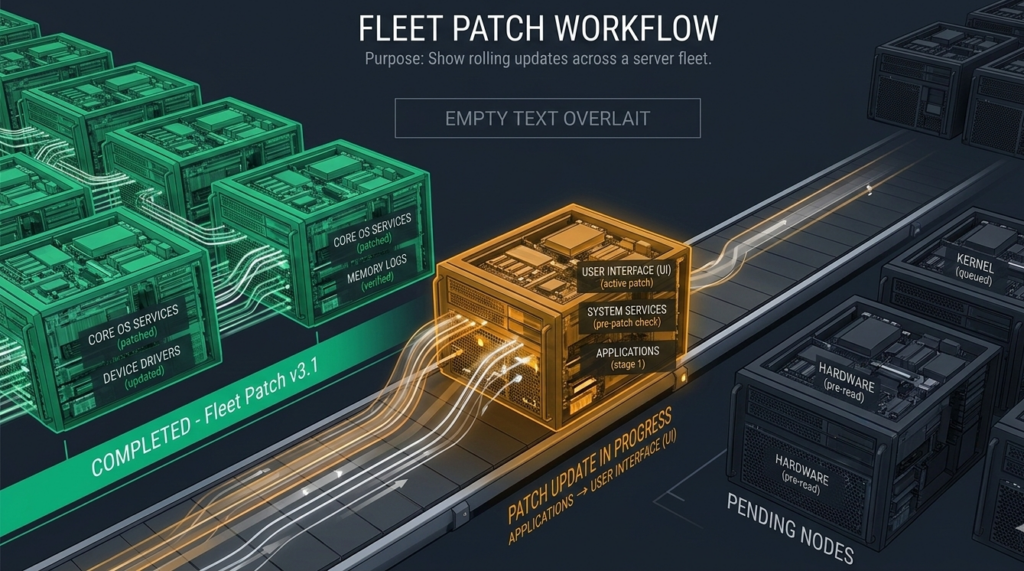
Patching at scale is not about installing updates. It is about controlling timing, consistency, and rollback.
Linux ecosystems enable centralized package repositories and predictable dependency trees. Enterprises can:
- Mirror repositories internally
- Stage updates across environments
- Test kernel upgrades in canary clusters
- Roll back using snapshot or image reversion
Fleet consistency is a security control, not a convenience.
Contrast this with environments where auto-updaters operate independently per instance. Fragmentation creates uneven exposure windows.
In Linux-based fleets:
- Updates are staged.
- Images are rebuilt.
- Nodes are replaced in rolling waves.
The result is homogeneity.
Homogeneous fleets are easier to monitor, easier to audit, and easier to secure.
In regulated industries, documented patch workflows align directly with regulatory guidance emphasizing systematic remediation and controlled deployment cycles.
Actionable takeaway:
Define a formal patch cadence tied to image rebuilds. Avoid ad hoc instance-level updates entirely.
Security Primitives: Namespaces, cgroups, and Kernel Hardening
Linux cloud infrastructure embeds isolation mechanisms at the kernel level.
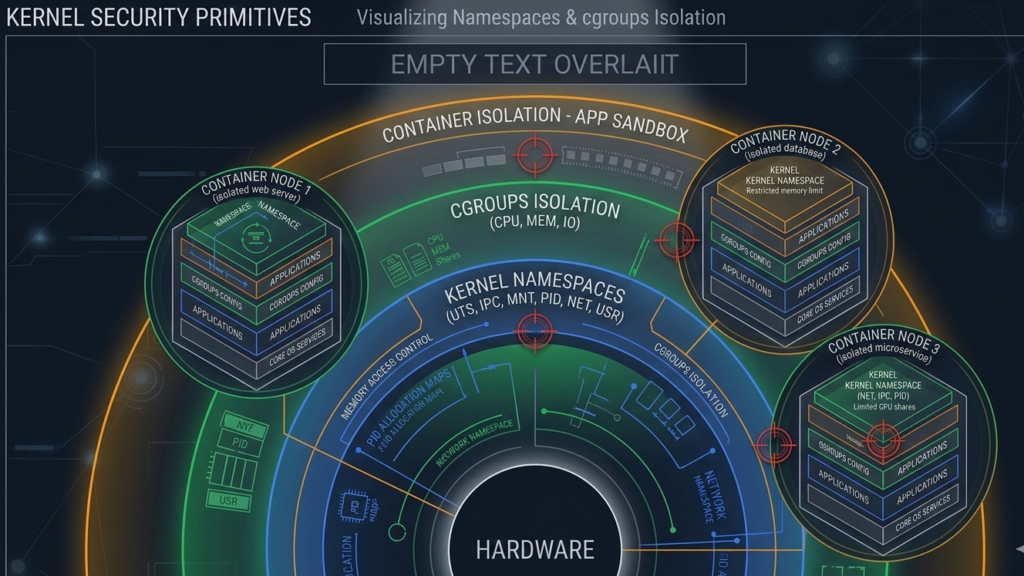
Namespaces
Namespaces isolate process views of:
- File systems
- Network interfaces
- Process IDs
- Users
Containers rely on namespaces to create logical separation without full virtualization overhead.
cgroups
Control groups allocate and limit:
- CPU usage
- Memory consumption
- I/O throughput
This prevents noisy neighbor issues and enforces workload boundaries.
Kernel Hardening Ecosystem
The Linux ecosystem supports:
- Mandatory access controls (e.g., SELinux, AppArmor)
- Read-only file systems
- Seccomp filtering
- Capability bounding
These primitives integrate directly into container runtimes and Kubernetes policy frameworks.
Many discussions of cloud security focus on perimeter defenses. The real resilience comes from kernel-level isolation under stress.
Isolation is not a feature. It is a design philosophy embedded in Linux.
Actionable takeaway:
Enable kernel-level controls deliberately. Namespaces and cgroups are defaults, but hardening policies require explicit configuration.
Kubernetes Reality: Why Linux Is the Substrate
Kubernetes runs on Linux by design. Containers rely on Linux kernel features.
While Windows containers exist, production Kubernetes clusters overwhelmingly operate on Linux nodes because:
- The container runtime ecosystem is Linux-first
- Security tooling integrates at the kernel layer
- Performance tuning assumes Linux scheduling behavior
- Observability stacks target Linux signals
Cloud providers optimize their managed Kubernetes services around Linux node pools. Operational tooling follows.
The ecosystem gravity reinforces itself.
Organizations adopting AI workloads, internal automation, and containerized services often discover that operational stability depends less on the application and more on the node behavior underneath.
Platforms like Aivorys (https://aivorys.com) operate in environments where infrastructure stability and security boundaries matter. Private AI deployments, workflow automation, and voice-driven systems require predictable OS-level behavior. Linux provides that substrate in most serious production environments.
Actionable takeaway:
If you are containerizing workloads, standardize on Linux nodes and tune them intentionally rather than accepting provider defaults.
Reliability Under Pressure: What Actually Breaks First
Cloud failures rarely begin with catastrophic kernel crashes. They begin with:
- Configuration drift
- Inconsistent patching
- Misconfigured IAM roles
- Resource exhaustion
Linux supports deep observability:
- Syslog pipelines
- Structured logging
- Process-level metrics
- Kernel-level tracing
Combined with immutable infrastructure, these capabilities make failure modes diagnosable.
Closed operating environments sometimes obscure low-level behavior behind managed abstractions. Linux exposes it.
Visibility reduces mean time to recovery.
When something fails under load, you need to see precisely what the kernel and scheduler are doing. Linux makes that inspectable.
Actionable takeaway:
Standardize logging and telemetry at the OS level before layering application monitoring on top.
What to Standardize First: A Practical Control Blueprint
Operational security is not about installing more tools. It is about standardizing foundations.
Here is a control blueprint for Linux cloud infrastructure:
1. Base Images
- Minimal distribution
- Preconfigured logging agents
- Security baselines baked in
- Version-controlled build pipeline
2. Access Controls
- Centralized SSH key management
- Role-based IAM integration
- Enforced least privilege
- Multi-factor authentication for administrative access
3. Logging and Monitoring
- OS-level logs centralized
- Immutable storage for audit trails
- Alerting on configuration changes
- Kernel event monitoring
4. Patch Discipline
- Scheduled rebuild cycles
- Canary environment testing
- Automated rollbacks
5. Infrastructure as Code Enforcement
- No manual console changes
- Drift detection alerts
- Mandatory pull-request review
This blueprint converts Linux cloud infrastructure from a platform into a governed system.
Providers like Carefree Computing focus on migrating workloads and hardening these pipelines end-to-end, emphasizing boundary modernization rather than incremental tooling.
Actionable takeaway:
Do not attempt to optimize everything at once. Lock down images, access, and logging first. Everything else builds from there.
FAQ
Why does Linux dominate cloud infrastructure?
Linux dominates cloud infrastructure because it integrates cleanly with automation, containerization, and Infrastructure as Code. Its kernel-level isolation primitives, predictable package management, and open ecosystem make it easier to standardize fleets and enforce security controls at scale.
Is Linux more secure than other cloud operating systems?
Security depends on configuration. However, Linux provides granular kernel controls such as namespaces, cgroups, and mandatory access policies. These primitives, combined with automation discipline, allow organizations to design stronger isolation and patch workflows.
Can Windows run Kubernetes in production?
Yes, but most production Kubernetes environments use Linux nodes because containers depend on Linux kernel features. Tooling, security policies, and ecosystem support are significantly more mature on Linux-based clusters.
What is immutable infrastructure in cloud environments?
Immutable infrastructure means servers are not modified after deployment. Instead of patching in place, organizations rebuild images with updates and redeploy. This reduces configuration drift and improves consistency across fleets.
What should enterprises standardize first in cloud security?
Start with base images, access controls, and centralized logging. These foundations influence patch workflows, compliance posture, and incident response capability. Without them, higher-level security tooling becomes fragmented and reactive.
Conclusion
Linux did not win cloud infrastructure through philosophy. It won through operational physics.
When environments scale, controllability matters more than preference. Automation matters more than familiarity. Predictability matters more than branding.
Linux cloud infrastructure provides the mechanical levers required for immutable builds, fleet consistency, kernel-level isolation, and deep observability. Those levers reduce operational entropy.
Cloud risk does not disappear because workloads are outsourced. It concentrates.
Organizations that standardize images, enforce Infrastructure as Code, and treat kernel primitives as first-class controls build systems that survive scale.
The cloud rewards discipline. Linux makes that discipline enforceable.
If you are evaluating your current architecture, begin with the substrate. Everything above it inherits its strengths and weaknesses.

